Designed to infect the Windows computer, the Diavol virus has been found wreaking havoc. Here we explain how the virus is transmitted and how you can stay protected from such threats.
As our dependency on gadgets, cloud storage, and other tools increases, the threat of cybercrime and sophisticated attacks grows exponentially. If not careful, you can be the next target, and personal information and financial details will be in the hands of bad guys distributing Diavol ransomware. To stay protected from such malicious attacks and virus threats, running an updated antivirus tool is recommended. If to date you don’t have an antivirus program installed and running you should get one and we suggest trying Systweak Antivirus. This excellent security tool for Windows comes with real-time protection, web protection, malware protection, exploit protection, a built-in firewall, and much more. Also, it scans startup items for infections and helps remove them. Using the powerful antivirus, you can schedule scans and perform different scanning – Quick Scan, Deep Scan or Custom Scan.
To get Systweak Antivirus, click the button below:
What is Diavol Ransomware?
In a warning issued by the Government of India, Diavol is a new strain of ransomware, transmitted to the Windows PC via email attachments containing URL links to OneDrive.
The ransomware, once installed, shuts down the device and demands a ransom to give back the control. It encrypts files and renames them .lock64 extension. Furthermore, it changes the desktop wallpaper and generates a README_FOR_DECRYPT.txt file containing data recovery information.
In addition to this, to scare users in the .txt file, hackers have mentioned that in absence of no payment their downloaded data will be published on the website controlled by the hackers.
Why is ransomware dangerous?
Unlike malware, virus, adware, and other malicious threats, ransomware along with stealing your data also decrypts it and kicks the victim out of the system. This means to get back access to data, the victim needs a decryption key which can only be retained after paying the ransom. However, if you don’t want to pay the ransom, then the only way to access data is by restoring the backup.
Note: Even if you pay the ransom, there is no guarantee that you will get the key. Therefore, paying cybercriminals is never recommended.
How ransomware infects the system?
Ransomware is distributed via malicious attachments sent in an email, product download from unreliable sources, software cracking tools, fake updaters, and opening malicious files. To trick users into opening such emails, cybercriminals often disguise them as a legitimate program or send them using employees or CEO ID that they have hacked.
| Name | Diavol virus |
| Threat Type | Ransomware, Crypto Virus |
| Encrypted Files Extension | .lock64 |
| Ransom Demanding Message | README_FOR_DECRYPT.txt |
| Free Decryptor Available? | No |
| Cyber Criminal Contact | Tor website |
| Detection Names | Avast (Win64:Trojan-gen), Combo Cleaner (Trojan.GenericKD.47184519), ESET-NOD32 (A Variant Of Win64/Filecoder.Diavol.A), Kaspersky (Trojan-Ransom.Win32.Encoder.ocs), Microsoft (Trojan:Win32/Sabsik.FL.B!ml), Full List Of Detections (VirusTotal) |
| Symptoms | Locking victims out of the computer and making data inaccessible. Also, the previously functional files now have a different extension (for example, my.docx.locked) and a message demanding ransom is displayed on the desktop. Payment is usually demanded in cryptocurrency (Bitcoin). |
| Distribution methods | Malicious ads, fake email attachments, torrent websites, macros, software crack. |
| Damage | Encrypts all files that can only be accessed after paying the ransom and getting a decryption key. Furthermore, Diavol also installs password-stealing trojans and malware infections. |
| Malware Removal (Windows) | To stay protected and remove possible malware infections, use Systweak Antivirus to scan the system and stay protected from such malicious threats. |
What Makes Diavol Risky?
Contrary to other ransomware Diavol uses user-mode Asynchronous Procedure Calls (APC) with an asymmetric encryption algorithm.
Lacks obfuscations
Saves the main routing within bitmap images which makes analysis difficult.
When executed on the victim’s machine, Diavol ransomware extracts the code from the images “PE resource section and loads it within a buffer with execution permission.
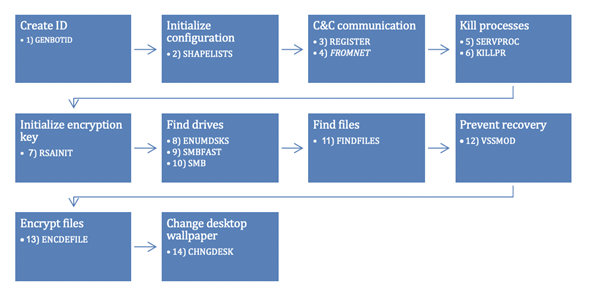
Before encrypting data, Diavol ransomware changes each encrypted Windows background to a black wallpaper with “All your files are encrypted! For more information, see the README-FOR-DECRYPT.txt message.

How to stay protected from ransomware infections?
- Always download programs and files from the official website.
- Never trust third-party sources for downloading any software.
- Keep software and operating system updated. To simplify the work, try Systweak Software Updater.
- Avoid opening email attachments and links received from unknown sources and senders in the email.
- Using reliable antivirus software programs can help. One of the best security tools isSystweak Antivirus.
- De-activate Remote Desk Protocol (RDP)
- If possible, place RDP behind a secured network.
- Network segmentation and segregation into security zones.
- Create a separate administrative network from business processes with physical controls and Virtual Local Area Networks.
With the help of these steps and by keeping the warning signs in mind, you can stay secure from Diavol and similar malware attacks.
We hope we made our point and helped understand what ransomware is, how dangerous it can be, and how to stay protected. If you have any further information or would like to share any other pointers to stay secure against such nasty threats, please do share the same in the comments sections. Also, to stay safe from malware, virus, and similar threats, we suggest running an updated antivirus like Systweak Antivirus. This will help keep our computers and data protected from nasty threats.



 Subscribe Now & Never Miss The Latest Tech Updates!
Subscribe Now & Never Miss The Latest Tech Updates!